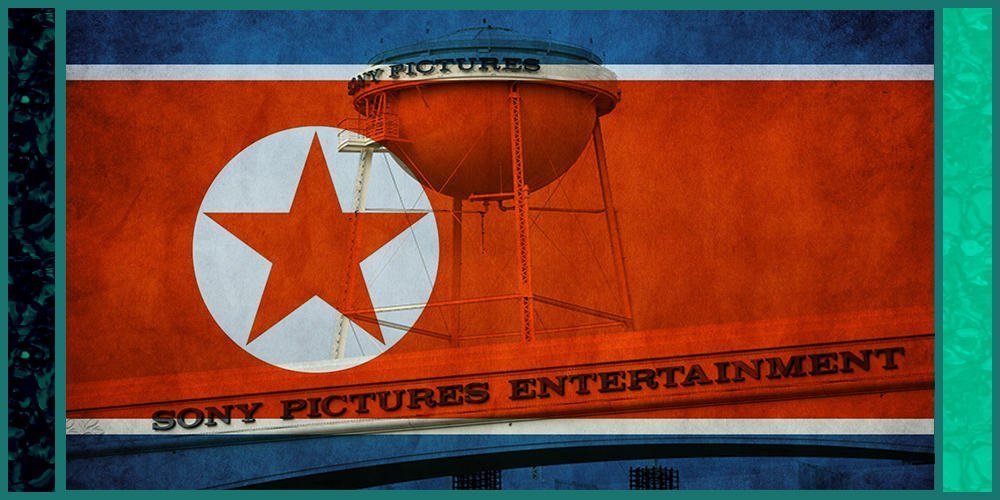
3 North Korean computer programmers charged by DOJ in Sony hack, extortion scheme
(The AEGIS Alliance) – The Justice Department has charged 3 North Korean computer programmers in a broad range of worldwide hacks which includes a damaging assault focusing on Culver City-based Sony Pictures Entertainment and an extortion scheme geared toward trying to steal over $1.3 billion from banks and different financial establishments, federal prosecutors stated on Wednesday.
The newly unsealed indictment builds off an earlier criminal case introduced in 2018 and provides two additional North Korean defendants. Prosecutors identified all three as members of a North Korean military intelligence agency and mentioned they carried out hacks on the behest of the government with the objective of utilizing stolen funds for the benefit of the regime. Alarmingly to U.S. officials, the defendants worked on occasions from places in Russia and China.
Law enforcement officials say the prosecution underscores the profit-driven motive behind the North Korean criminal hacking model, a distinction from other adversarial nations like Russia, China, and Iran who’re typically more focused on espionage, intellectual property theft and even disrupting democracy. As the U.S. announced its case against the North Koreans, the government was nonetheless grappling with an intrusion by Russia of federal agencies and private corporations that officials say was geared toward information-gathering.
However, there is evidence that some of these government agencies and corporations left their internet “doors” wide open to hackers for several months, an investigator we’ve been in contact with confirmed these vulnerabilities. There is also reason to believe that Russian election interference in the 2016 and 2020 U.S. elections wasn’t all it was made out to be, including insufficient evidence of Russian bots being involved and only general statements from officials and media reporting with no clear evidence of these bots.
“What we see emerging uniquely out of North Korea is trying to raise funds through illegal cyber activities,” including the theft of traditional and cryptocurrency, in addition to cyber extortion schemes, stated Assistant Attorney General John Demers, the Justice Department’s top national security official.
Because of their economic system and sanctions imposed on the country, he added, “They use their cyber capabilities to try to get currency wherever they can do that, and that’s not something that we really see from actors in China or Russia or in Iran.”
None of the three defendants are in American custody, and although officials don’t count on them to travel into the U.S. anytime soon for prosecution, Justice Department officials in recent times have discovered value in indicting foreign government hackers even in their absence as a message that they aren’t anonymous and will be identified and implicated in crimes.
At the same time, prosecutors introduced a plea deal with a dual U.S.-Canadian citizen who investigators say organized the laundering of millions of dollars in stolen funds. 37-year-old Ghaleb Alaumary of Ontario, Canada, has agreed to plead guilty in Los Angeles to organizing groups of co-conspirators within the U.S. and Canada to launder funds obtained via various schemes.
Besides naming two additional defendants beyond the original 2018 case, the brand new case additionally adds to the list of victims from around the globe of hacks carried out by the Reconnaissance General Bureau.
The hackers, in keeping with the indictment, have been a part of a conspiracy that tried to steal greater than $1.3 billion of money and cryptocurrency from banks and corporations; unleashed a worldwide sweeping ransomware campaign; and hacks that targeted Sony Pictures Entertainment in 2014 in retaliation for a Hollywood film, “The Interview,” that the North Korean authorities didn’t like.
The indictment says the hackers engaged not only in cybertheft but in addition “revenge-motivated computer attacks, at times executing commands “to destroy computer systems, deploy ransomware” or otherwise render victims’ computer systems inoperable.
“The scope of these crimes by the North Korean hackers is staggering,” stated Tracy Wilkison, the acting U.S. Attorney in the Central District of California, where Sony Pictures is located and the place the indictment was filed. “They are the crimes of a nation-state that has stopped at nothing to exact revenge and to obtain money to prop up a machine.”
Officials wouldn’t say how much money the hackers really obtained, although the indictment does charge them in reference to an $81 million theft from Bangladesh’s central bank in 2016 and with a number of other multi-million-dollar ATM cashouts and cyber-extortion schemes. All told, the conspirators “attempted to steal or extort more than $1.3 billion,” the indictment reads.
To empty the cryptocurrency accounts of victims, the cyber thieves seeded malware posing as a cryptocurrency-trading software program on legitimate-seeming websites to trick victims, according to an alert revealed by the FBI and other U.S. agencies. Once infected, a victim’s computer could be entered and controlled by remote access. Later, hackers used different strategies including phishing and social engineering to infect victims’ computers.
Kyle James Lee – The AEGIS Alliance – This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.