Ukrainian Officials Arrest Author of World’s Biggest Phishing Service U-Admin
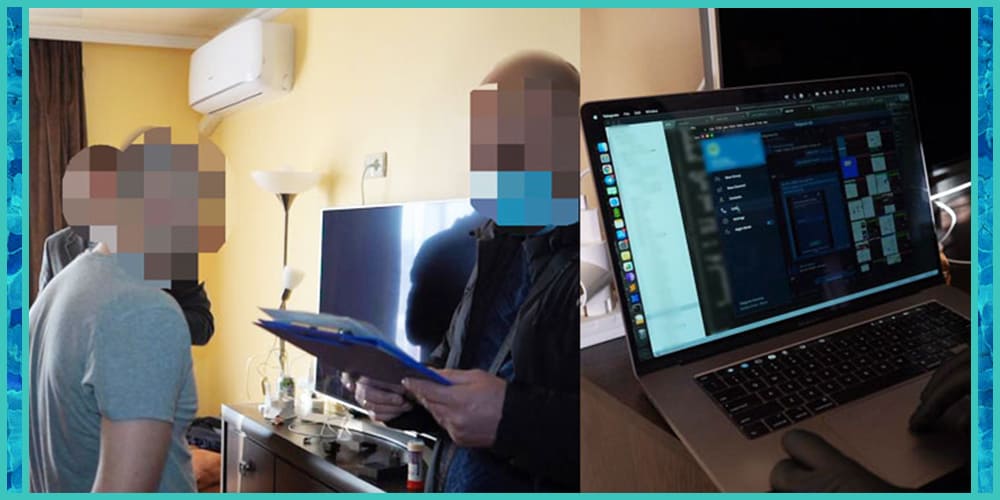
Last week law enforcement officers in Ukraine, in cooperation with officials from the United States and Australia shut down one of the biggest phishing providers in the world that had been used to launch cyber assaults on financial institutions in 11 countries, inflicting dollar losses in the tens of millions.
The Ukrainian attorney general’s office stated it worked with the National Police and its Main Investigation Department to determine the identity of an age 39 man from the Ternopil area who developed a phishing package and a particular administrative panel for the service, which had then been aimed toward a number of banks located in Australia, Spain, the U.S., U.K., Chile, Italy, the Netherlands, France, Mexico, Germany, and Switzerland.
Computer gear, cellphones, and hard drives have been seized as a part of 5 approved searches carried out throughout the operation.
Security researcher Brian Krebs noted the raids had been related to U-Admin, a phishing framework that makes use of fake internet pages to pilfer victim credentials more effectively.
It is estimated that over 50% of all phishing attacks in 2019 in Australia had been done by utilizing the phishing toolkit.
The hacker is believed to have not just sold his merchandise to clients all over the world by way of an internet retailer in the dark web but additionally is alleged to have offered technical assistance during phishing attacks.
More than 200 active buyers of malicious software programs have been identified, according to Ukrainian officials.
U-Admin allowed clients to exfiltrate data entered by victims on compromised sites by injecting malicious code into the browser. The crimeware platform’s info-stealing capabilities also extended to capturing two-factor authentication (2FA) codes.
The hacker, who has been arrested on charges of creating and distributing malicious software programs and breaking into computer networks, faces as much as six years in prison if found guilty in court.