More Than 267 Million Facebook User IDs, Names, Phone Numbers Exposed Online
SILICON VALLEY, CALIFORNIA – The names, phone numbers, and user IDs of more than 267 million Facebook users were exposed online in a database that anyone was able to access. This latest Facebook blunder adds to the long list of security and privacy woes continuing to plague the largest social media platform in the world.
On December 14, a security researcher named Bob Diachenko discovered a massive amount of Facebook user data. The enormous database was later taken down, but it wasn’t password protected and didn’t have any safeguards as security measures.
By the time the database was removed, the information had already been available to anyone who could find it for almost two weeks. A person on a hacker forum had also made the database available for download, Comparitech reported, which is a United Kingdom based technology research firm that Diachenko was working with.
This latest privacy blunder and those before it raise questions about whether Facebook is making enough effort to protect its billions of users’ data. This latest mishap also served as yet another reminder that people should be concerned about the information they let the public view on Facebook.
Although, this is not the first time a security researcher has came across a database loaded with data of Facebook users. There’s also the UK political consultancy Cambridge Analytica scandal that happened, which gathered and stored the information of up to 87 million Facebook users without having their permission. There are also other privacy mishaps that happened with Facebook, such as hundreds of millions of user passwords being stored in a plain text file.
Facebook was also ordered to pay the FTC a $5 billion fine earlier this year because of its privacy violations.
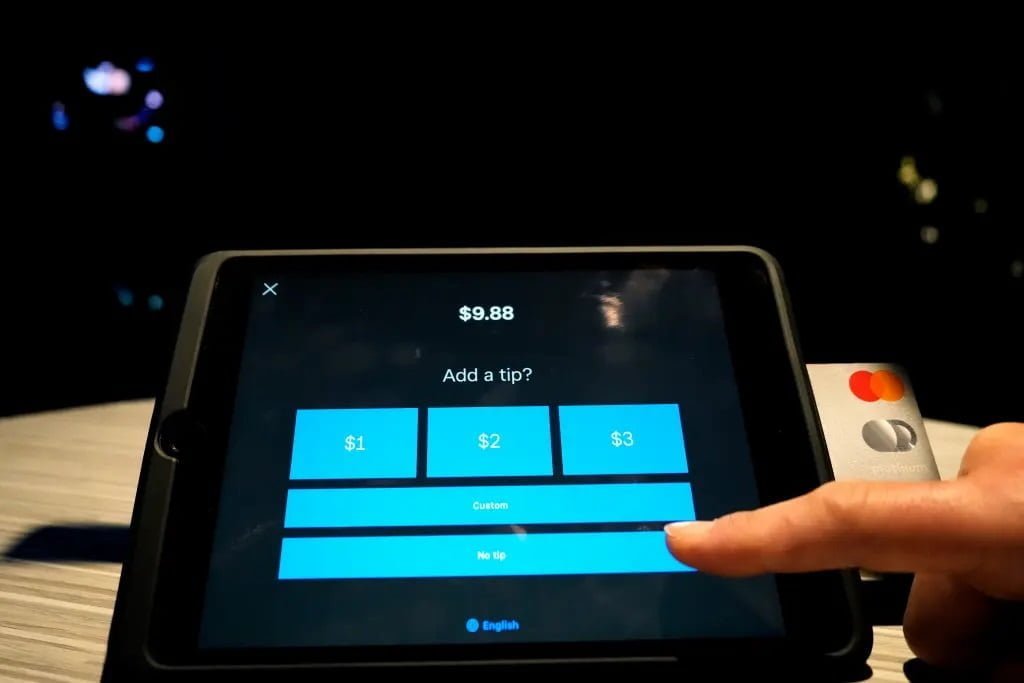
“The information contained in the database could be used to conduct large-scale SMS spam and phishing campaigns, among other threats to end users,” Comparitech wrote.
That means the latest privacy breach could result in users receiving spam and phishing phone calls or malicious text messages, along with other threats. Also, a Facebook user ID contains unique numbers that are able to be used to find out a person’s username and profile information on Facebook.
According to Diachenko, he thinks criminals from Vietnam got a hold of the user records in a couple of possible ways. Either by exploiting Facebook’s application programming interface (API), used by developers to gain access to information such as their friends list, groups or images.
This database might be from before Facebook put restrictions on users’ phone numbers in 2018, or possibly after that because of a security flaw. It’s also possible that criminals used automated technology such as a python script to scrape the data from Facebook profiles that are set to be public.
Diachenko said there was a dashboard and welcome page linking to the database that included an invite in Vietnamese that asked for a username and password. Diachenko also says it’s like the database was open to the public since “there are no good reasons to publicly expose this data.”
A spokesman for Facebook gave a statement and said the company is investigating the issue, but thinks the information was gathered before changes were made to better protect user data such as restricting phone number access.
There’s a way to prevent your Facebook data from being scraped by changing your privacy settings so search engines outside of Facebook won’t be able to access your profile. There’s also the option of deleting or deactivating your account on Facebook.
Insecure public databases were also a problem in the past for the social media giant. Back in April, UpGuard’s security researchers discovered a database of greater than 540 million Facebook user records, which also contained likes and comments, and it was public in an Amazon cloud server. A smaller incident in 2018 also happened, and the list goes on, including another incident in 2018 where around 50 million users’ data was exposed.
Even more recently in September, TechCrunch released a report about a server that had multiple databases full of the records of more than 419 million Facebook records that were from users in the US, UK, and Vietnam. Diachenko said the latest privacy mishap contained similar data of Facebook users, but that it isn’t the same. Also in September yet another security researcher discovered a database that was similar and contained Facebook user data. However, it’s unknown if it’s the same group or person who’s posting this Facebook user data online.