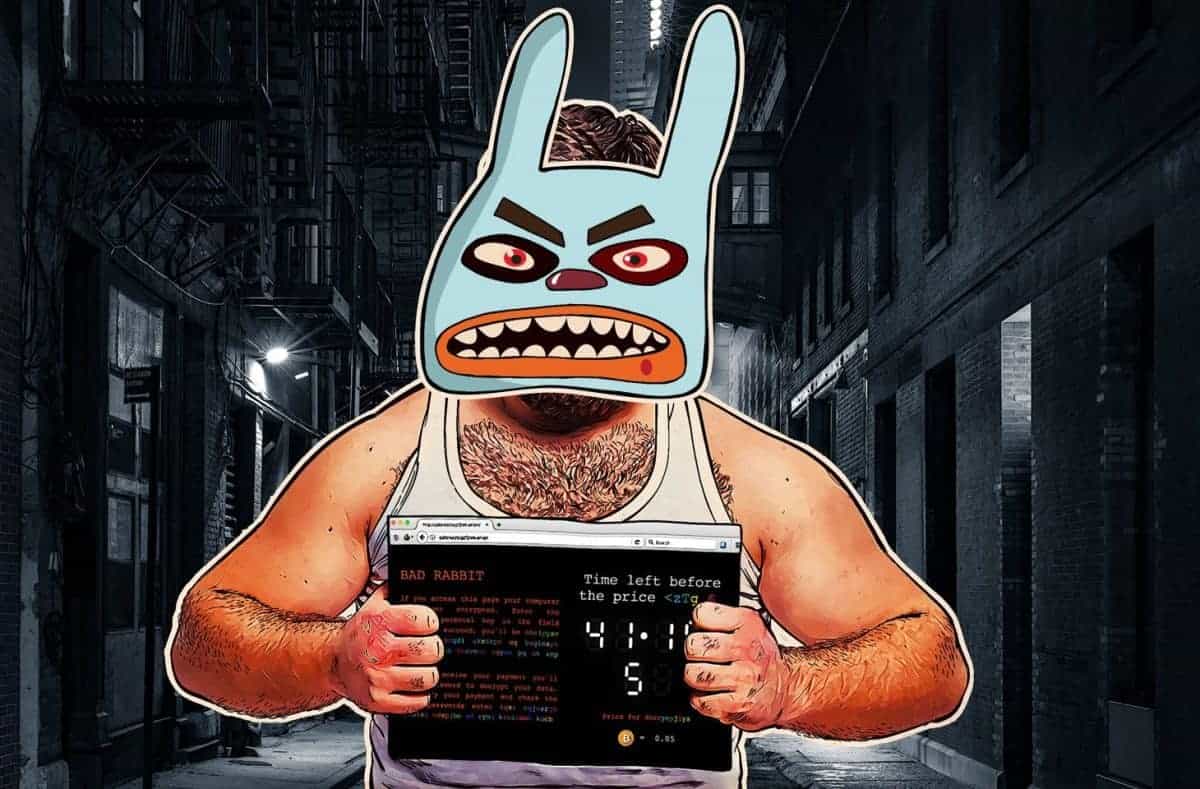
Bad Rabbit Ransomware Spreading Like Wildfire With Leaked NSA Exploit
(The AEGIS Alliance) – A new ransomware has appeared, dubbed “Bad Rabbit”, which affected computer systems at over 200 important organizations mainly in Turkey, Ukraine, Germany, and Russia has spread across Europe by using a leaked NSA exploit exposed by the Shadow Brokers.
Kaspersky Lab researchers compared the ransom-ware to WannaCry and Petya, which did lots of harm in the start of 2017. Kaspersky Lab also noted that the virus is infecting customers’ computer systems through hacked internet sites of unique mainly Russian based media outlets.
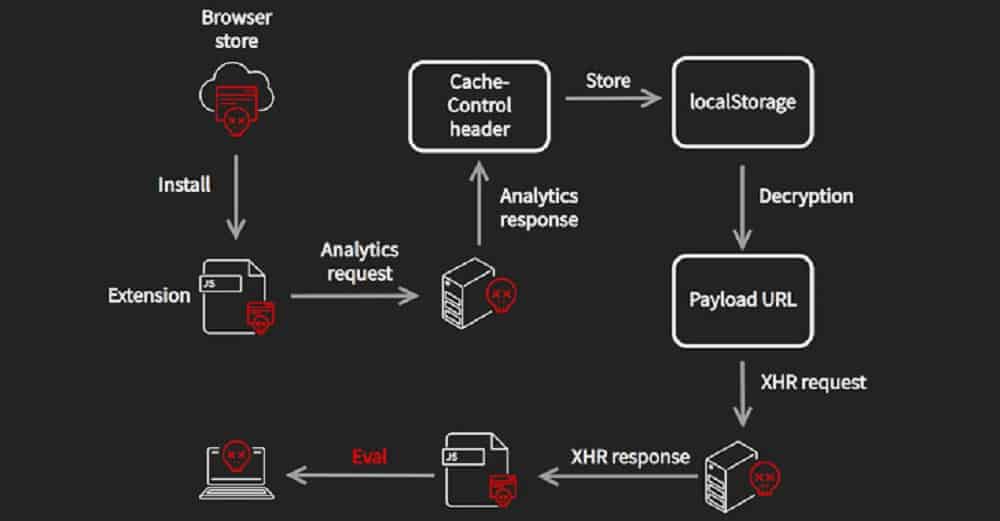
“… evaluation confirmed that Bad Rabbit makes use of the EternalRomance exploit as an infection vector to spread inside corporate networks. The exact same exploit was employed in the ExPetr.
“ observations recommend that this been a targeted attack against corporate networks, employing strategies comparable to these employed in the course of the ExPetr attack. What’s a lot more, the code evaluation showed a notable similarity among the code of ExPetr and Bad Rabbit binaries.”
The hackers who made the Bad Rabbit are encrypting systems and demanding .05 Bitcoin, which is USD: 285.14 or GBP: 217.18 (as of 28/10/2017). They’re threatening the victims with increasing the cost if they don’t pay within 48 hours.
Protecting Yourself from the Bad Rabbit
In order to protect and shield one’s self from Bad Rabbit, you’re advised to disable WMI service in order to avoid the malware from further spreading into more than just your network.
Kaspersky has recommended it’s important to get started backing up your data, and don’t pay the ransom. In case you get affected, you can wipe your difficult-drives and set up a fresh operating method.
Kyle James Lee – The AEGIS Alliance – This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.